Imagine hiring an intern who works 24/7, asks for zero salary, and executes complex tasks on your laptop while you sleep. That is the promise of OpenClaw (formerly known as MoltBot and ClawdBot).
It sounds like a dream for productivity, doesn’t it? But before you, or your employees, install this “miracle” agent, we need to talk about the critical security flaws hiding behind the hype.
Table of Contents
ToggleWhat Is OpenClaw?
OpenClaw is an open-source, local AI agent created by Peter Steinberger that acts as a “digital Chief of Staff.” Unlike standard chatbots, OpenClaw runs locally on your machine and uses the Model Context Protocol (MCP) to connect directly to your files, terminal, and apps like WhatsApp and Slack.
Key Insight: OpenClaw is often described as a “new weird friend” that lives on your computer. However, security researchers have labeled it a security nightmare because it grants an AI agent shell access without built-in authentication.
The Name Game: ClawdBot → MoltBot → OpenClaw
If you are confused by the name, you aren’t alone. The project has undergone a rapid rebranding evolution:
- ClawdBot (Nov 2025): The viral launch name.
- MoltBot (Jan 2026): A brief rebrand to avoid trademark disputes with Anthropic.
- OpenClaw (Present): The final, official name as of late January 2026.
While the name has changed, the underlying engine remains the same: a powerful, unrestricted tool that operates outside traditional security perimeters.
The New “Shadow AI” Reality
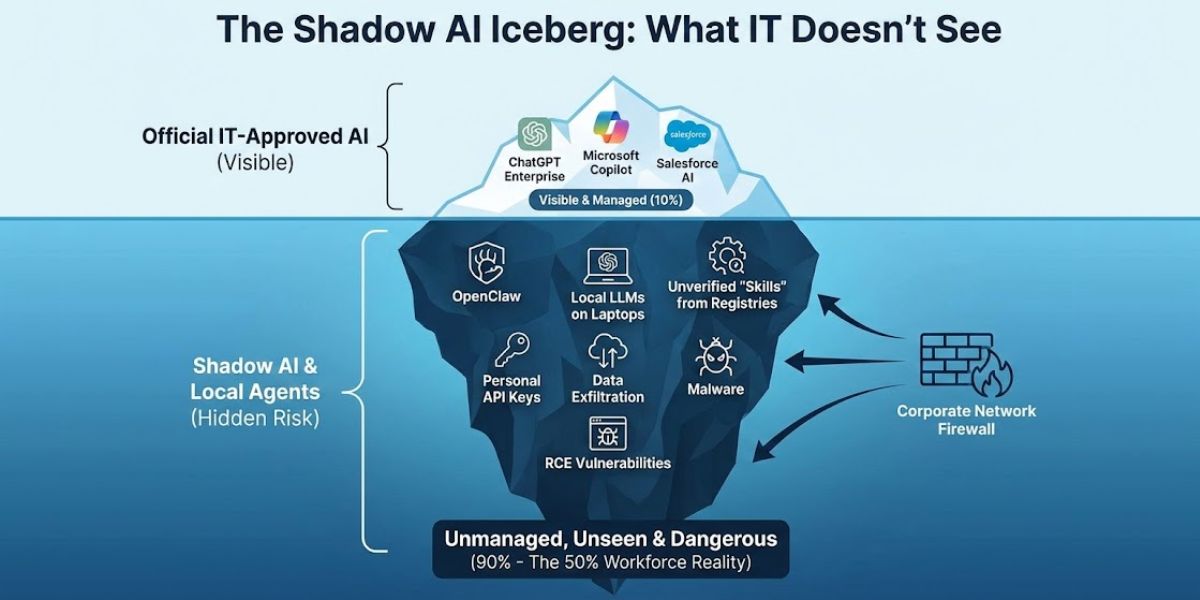
At Azence, we champion automation that helps SMBs scale. But OpenClaw has become the face of a dangerous new trend: Shadow AI.
According to a recent study, 50% of workers now use unapproved AI tools to get work done, and most admit they wouldn’t stop even if their company banned them.
The risk isn’t just the software; it’s the ecosystem.
- Malicious Skills: Hackers are uploading compromised “skills” to registries like ClawHub. A recent report found malicious skills disguised as crypto tools designed to drain wallets.
- One-Click Compromise: Security audits have flagged vulnerabilities where a single malicious link can trigger One-Click Remote Code Execution, granting attackers full control over the host machine.
The Bottom Line: Deploying “naked” open-source agents like OpenClaw without a security layer is dangerous. If your team is installing this on company devices without a proper IT governance strategy, you are bypassing your firewalls and inviting a data disaster.
For a safer approach to AI staffing, read our guide on ChatGPT Agents vs. Human Operators.
> *Watch: Creator Peter Steinberger demonstrates the “agentic” capabilities that made OpenClaw viral.*
Why Is OpenClaw Viral? (The Good Stuff)
It is easy to see why OpenClaw (formerly MoltBot / ClawdBot) went viral overnight. In a world of expensive subscriptions and walled gardens (refers to closed, controlled technology ecosystems where the platform provider tightly restricts what software, data, or services can interact with it), this tool feels like a breath of fresh air for the tech-savvy. It offers a level of control and power that usually costs thousands of dollars a month, all for the price of a little setup time.
The Appeal: Self-Hosted AI for Business
For the tinkerers and the growth-obsessed crowd, solopreneurs and small teams looking to scale, OpenClaw feels like finding a cheat code. The appeal comes down to three things: ownership, flexibility, and cost.
Instead of relying on a cloud platform that might change its pricing or privacy policy tomorrow, OpenClaw runs locally on your own machine. It typically uses Docker containers to create a sandbox where the AI operates, meaning you aren’t renting the agent; you own the instance.
Key Difference: Unlike SaaS tools, OpenClaw is model-agnostic. You can plug in API keys for Anthropic’s Claude, OpenAI’s GPT-4, or Google’s Gemini, depending on which model is smartest or cheapest that day.
For a lean startup, this kind of self-hosted AI is the ultimate efficiency hack, no monthly fees, just raw compute power.
The Secret Sauce: Real “Agency” & MCP
What makes OpenClaw different from ChatGPT? It doesn’t just chat; it does.
It leverages the Model Context Protocol (MCP) to connect directly to your files, terminal, and apps. This allows it to interact with interfaces like a human would.
Imagine handing off your most tedious tasks to a machine that never gets tired. In one famous example, creator Peter Steinberger demonstrated OpenClaw logging into the British Airways website, finding his passport details, and checking him into a flight automatically.
Users are deploying OpenClaw to:
- Execute Complex Workflows: Like the airline check-in example, navigating multi-step web forms without human input.
- Code Autonomously: Finding a bug in a Git repository, fixing the code, and committing the patch.
- Manage IoT Devices: Controlling smart home devices like Philips Hue lights and Sonos speakers directly from a chat interface.
At Azence, one of our core values is “Efficiency through Innovation”. OpenClaw aligns perfectly with that vision. It promises to simplify your workflow so you can whistle while you work.
But as with any powerful tool, how you use it matters just as much as what it can do.
The “Shadow AI” Problem: It’s Not Just the Bot, It’s the Supply Chain
We have established that OpenClaw is powerful. But in the world of cybersecurity, “powerful” and “secure” are rarely the same thing.
The risk isn’t just the agent itself; it’s the ecosystem around it. We are seeing the rise of AI Supply Chain Attacks, where the danger comes from the “skills” your employees install.
The “Naked” Agent & One-Click Remote Code Execution
In its default state, OpenClaw is what we call a “naked” agent, built for speed, not self-defense. Security researchers have flagged CVE-2026-25253, a critical vulnerability (CVSS 8.8) that allows for Remote Code Execution (RCE).
The Threat: A single malicious link sent to your employee can trick the locally running OpenClaw agent into executing code. This gives attackers full control over the host machine without the user ever typing a password.
The “ClawHub” Trap: Malware in the Marketplace
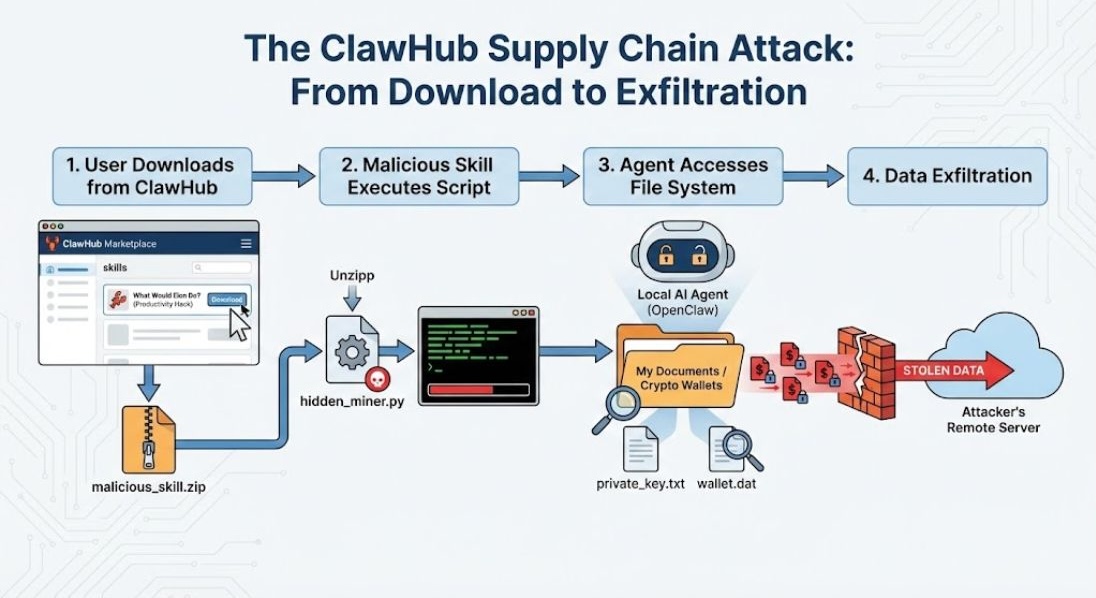
Just like your phone has an App Store, OpenClaw has ClawHub (formerly MoltHub), a registry where users can download new “skills” for their agent.
This is the new frontier for hackers. A recent report by Tom’s Hardware found 14 malicious skills uploaded to the registry in a single month.
- The “What Would Elon Do?” Hack: One popular skill promised to mimic Elon Musk’s management style. In reality, it contained a script designed to scan the user’s file system for crypto wallet keys and exfiltrate them to a remote server.
- Silent Exfiltration: Because OpenClaw has legitimate access to your files and internet, these malicious skills can steal sensitive company data without triggering standard antivirus software.
The Reality Check: Tens of Thousands Exposed
This isn’t just a theoretical risk. In a recent internal review, our cybersecurity lead, Torry, noted that tens of thousands of OpenClaw setups have struggled with security, often accidentally exposing internal systems to the open web due to improper sandboxing.
These employees aren’t trying to hack the company; they are trying to be efficient. But without strategic oversight, that good intention creates a backdoor.
As we’ve seen with third-party app risks, innovation should not come with an open invitation to hackers.
3. How to Tame the Beast: The Azence Security Protocol
So, you have a powerful tool that your team loves, but it’s potentially dangerous. What is the move? Banning it usually just drives it underground.
The Azence OpenClaw Protocol
If your organization is going to leverage agents like OpenClaw, you cannot treat it like a laptop app. Our cybersecurity experts advise moving away from local installations entirely.
Follow these 3 Golden Rules:
- Centralize & Containerize:
- Stop Local Hosting: Do not let employees run OpenClaw on their personal laptops.
- The “Server” Strategy: Deploy OpenClaw on a centralized, containerized server (managed by your IT team or an MSP) with strict Role-Based Access Controls (RBAC). This ensures that if the agent goes rogue, it is trapped in a box, not roaming your CEO’s hard drive.
- Supply Chain Hygiene (The “No-Slop” Rule):
- Audit Your Skills: Do not download “skills” blindly from ClawHub. Treat every skill like an executable file from a stranger.
- Code Review: Before installing a skill, open the file. If you see obfuscated code or calls to unknown external servers, delete it immediately.
- Network Isolation:
- The “Air Gap”: Ensure the hosting server is behind a secure VPN (like Tailscale) or an authenticated reverse proxy. Never expose the raw API ports to the public internet.
Key Takeaway: Secure OpenClaw by moving it off laptops and onto managed infrastructure, centralized, containerized, and controlled.
Strategy First, Tools Second
At Azence, we believe in using technology to scale, not to stress. Tools like OpenClaw are incredible, but they require infrastructure, not just installation.
We don’t manage the servers, but we help you design the digital strategy that makes them profitable. Whether it’s validating your market approach or defining an SEO roadmap for your new AI tools, we help you whistle while you work safely.
Book a Project Review with Azence today to ensure your innovation strategy is built on solid ground.
Conclusion: The Future is Agentic (But Don’t Let It Bite You)
OpenClaw is proof that the future of AI is accessible, agentic, and incredibly exciting. We are moving away from chatting with bots and toward agents that actually do the work for us. That is a future we should embrace.
But “accessible” should never mean “insecure.”
True innovation is only efficient if it is sustainable. You can automate a thousand tasks today, but if it leads to a ClawHub supply chain attack tomorrow, you haven’t saved time, you have just created a crisis. A compromised network is the exact opposite of efficiency.
The Final Takeaway: Go ahead and download OpenClaw to organize your Spotify playlists or manage your personal grocery list on a spare laptop. Have fun with it. But for your business? Do not gamble with your data.
Ready to Scale Without the Chaos?
Curious how to integrate AI tools into your marketing workflow without breaking your business?
Book a Project Review with Azence today. Let’s build something safe, smart, and scalable.
Frequently Asked Questions about OpenClaw
What is the difference between OpenClaw, MoltBot, and ClawdBot?
They are the same tool. The project started as ClawdBot (Nov 2025), was briefly renamed MoltBot (Jan 2026) to avoid trademark issues with Anthropic, and is now officially called OpenClaw. It is an open-source, local AI agent.
Is OpenClaw safe for my business?
Not in its default configuration. Security researchers have identified “One-Click RCE” vulnerabilities that allow attackers to take over the host machine via a malicious link. It should never be run on a company network without strict isolation and security protocols.
What is “Shadow AI”?
Shadow AI refers to employees using unapproved AI tools (like OpenClaw) on company devices to automate tasks. A 2026 study found that 50% of workers use these tools without IT knowledge, bypassing security protocols and creating hidden data leak risks.





